Middle East Cybersecurity Market Share, Opportunities 2026-2034
REPORT DETAILS
REPORT DETAILS
ABOUT THIS REPORT
Market Statistics
What is the Current Market Size?
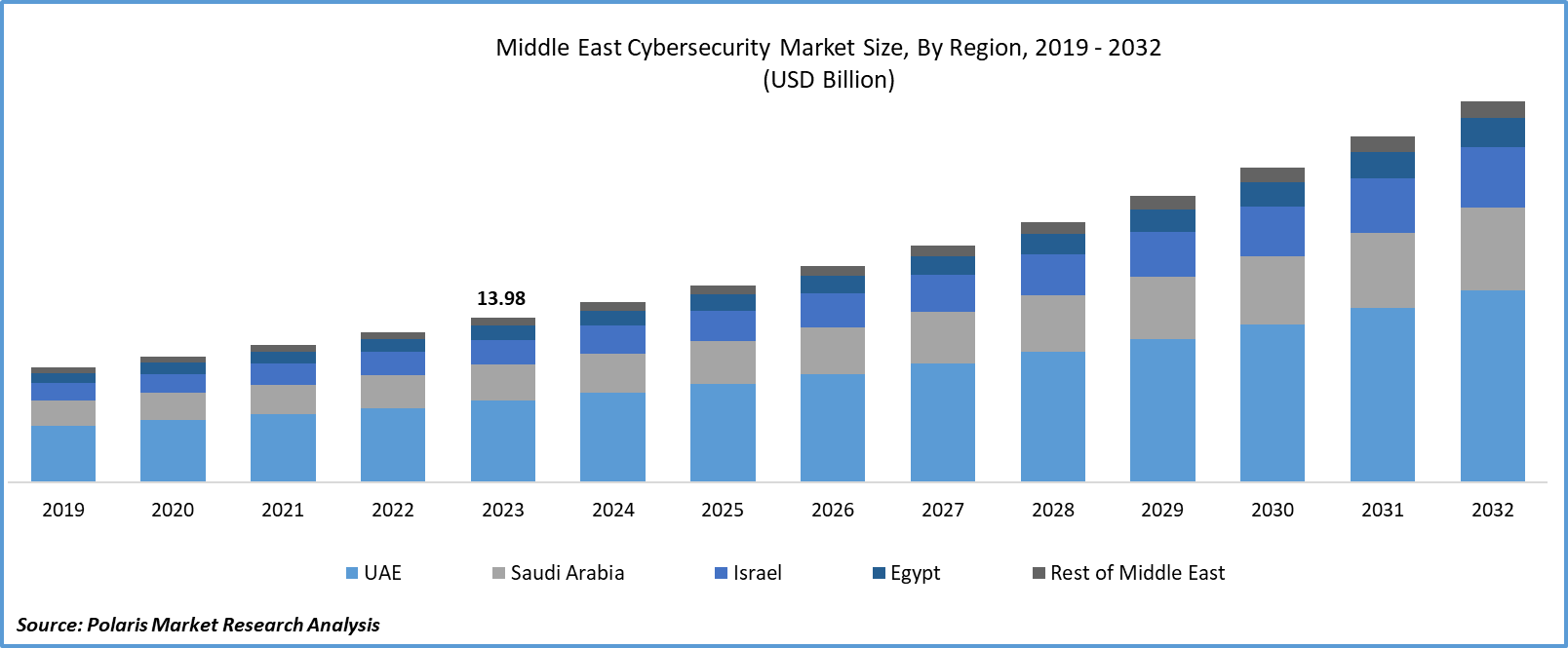
The middle east cybersecurity market size was valued at USD 16.78 billion in 2025. The market is anticipated to grow from USD 18.40 billion in 2026 to USD 39.31 billion by 2034, exhibiting a CAGR of 10.00% during the forecast period.
Market Statistics
- 2025 Market Size: USD 16.78 billion
- 2034 Projected Market Size: USD 39.31 billion
- CAGR (2026-2034): 10.00%
- UAE: Largest market in 2025
Industry Trends
Cyber security in the Middle East is rapidly growing, driven by the increasing demand for advanced security solutions to protect critical infrastructure, government agencies, and businesses from cyber threats. The rise of digital transformation and smart city initiatives across the region has further accelerated the need for robust cybersecurity measures. Governments and organizations are investing heavily in developing their cybersecurity capabilities to safeguard against cyber-attacks, data breaches, and other malicious activities that can compromise national security, intellectual property, and sensitive information.
Factors like the increasing number of cyber threats faced by the region are fueling the growth of the market. Cybercriminals view the Middle East as a lucrative target, and the region is frequently subjected to sophisticated attacks designed to compromise critical infrastructure and steal sensitive information. As a result, organizations and governments are recognizing the need to invest in advanced cybersecurity solutions to protect themselves against these threats. Another factor is the growing Middle East cybersecurity market trends toward digital transformation and smart city initiatives. Many governments in the Middle East are investing heavily in modernizing their infrastructure and adopting new technologies to improve efficiency and enhance citizen services.
The middle east cybersecurity market report details key market dynamics to help industry players align their business strategies with current and future trends. It examines technological advances and breakthroughs in the industry and their impact on the market presence. Furthermore, a detailed regional analysis of the industry at the local, national, and global levels has been provided.
To Understand More About this Research: Download Sample Report
However, these initiatives also introduce new security risks, making it essential for organizations to implement robust cybersecurity measures to protect their networks and systems. The region faces several challenges for the growth of the market, including the limited budget allocated to cybersecurity and complexity. Overall, the market is expected to grow significantly due to the rising number of cyber threats, digital transformation, regulatory compliance, cloud adoption, and the need for data privacy.
Key Takeaways
- The UAE dominated the Middle East cybersecurity market worth in 2025
- By deployment mode category, the on-premise segment accounted for the largest Middle East cybersecurity market share
- By end-user category, the healthcare segment is experiencing substantial growth over the forecast period
What are the market drivers driving the demand for the Middle East Cybersecurity market?
The growing number of cyber-attacks is driving the Middle East cybersecurity market growth.
As more businesses and organizations in the region adopt digital technologies, they become increasingly vulnerable to cyber threats. Cybercriminals are exploiting these vulnerabilities to steal sensitive information, disrupt operations, and cause financial losses. This has led to a surge in demand for cybersecurity solutions and services that can help protect against these threats. The rising number of cyber-attacks, coupled with the increasing adoption of digital technologies, is creating a strong need for cybersecurity solutions and services in the region. This growth is also driven by factors such as stringent government regulations, the increasing use of mobile devices, and the growing trend of remote working. As a result, organizations in the Middle East are investing heavily in cybersecurity solutions and services to protect their networks, data, and assets from cyber threats. Owing to all these factors, the market in the Middle East region is growing significantly.

Which factor is restraining the demand for Middle East Cybersecurity?
Complexity in integration with existing systems is hampering the Middle East Cybersecurity market growth.
The complexity of integrating cybersecurity solutions with existing systems is a significant challenge faced by the market. Many organizations in the region have systems that were not designed with security in mind, making it difficult to integrate modern cybersecurity solutions. This leads to compatibility issues, data fragmentation, and increased operational costs.
Also, the lack of interoperability between different systems creates security gaps, making it easier for attackers to exploit vulnerabilities. Also, the integration process can be time-consuming and resource-intensive, requiring significant investments in training, staffing, and infrastructure. This complexity can deter organizations from investing in cybersecurity solutions, hindering the growth of the market.
Middle East Cyber Security Breaches
| Year | Country | Incident Description |
| 2021 | Saudi Arabia | Detected 385K+ cyber-attacks during G20 Presidency; 361 threats analyzed and handled, targeting events and infrastructure |
| 2023 | Jordan – National Cyber Security Center (NCSC) | ~2,455 cybersecurity events reported. Official cybersecurity centre release indicates an 80% increase in reported cybersecurity events compared to 2022. |
| 2024 | UAE Cyber Security Council & CPX (government-linked report) | Exposed vulnerabilities, incident vectors tracked. Official State of UAE Cybersecurity Report highlights over 223,800 exposed assets and ongoing threat landscape involving unpatched systems and sophisticated attacks. |
| 2025 | UAE | Thwarted ransomware attacks on strategic sectors (public/private); part of 200K daily cyberattacks from 14 countries, targeting government (30%), finance (7%) |
| 2025 | UAE | Countered sophisticated AI-driven breaches including deepfakes, social engineering, malware; hackers identified and neutralized |
Report Segmentation
The market is primarily segmented based on component, deployment mode, organization size, security type, solution, end-user, and country.
| By Component | By Deployment Mode | By Organization Size | By Security Type | By Solution | By End-User | By Country |
|
|
|
|
|
|
|
To Understand the Scope of this Report: Request Customization
Category Wise Insights
By Deployment Mode Insights
Based on deployment mode analysis, the market is segmented on the basis of on-premise and cloud-based. The on-premise segment held the largest Middle East cybersecurity market share due to the region's preference for cybersecurity solutions on their premises rather than relying on cloud-based services. This is because of their willingness to maintain control over their data and security infrastructure, as well as ensure that sensitive information is not stored outside of their internal networks.
Also, on-premise deployments offer greater customization and flexibility, allowing organizations to tailor their cybersecurity solutions to meet specific business needs. On-premise deployments are often seen as more secure than cloud-based solutions, as they are less vulnerable to potential breaches or attacks that may occur through shared infrastructure. As a result, many organizations in the Middle East choose to invest in on-premise cybersecurity solutions, which has contributed to the dominant market share of this segment.
By End-User Insights
Based on end-user analysis, the market has been segmented on the basis of BFSI, defense and government, healthcare, IT & telecom, retail, travel and hospitality, and others. The healthcare sector is anticipated to drive significant growth in the market over the next few years due to the increasing adoption of digital technologies and electronic health records (EHRs) by healthcare organizations, which have become vulnerable to cyber-attacks, data breaches, and other security threats. As a result, there is growing concern among healthcare providers about protecting patient data and sensitive information from unauthorized access or malicious attacks. Also, the pandemic has further accelerated the need for robust cybersecurity measures in the healthcare industry, as telemedicine and remote consultations have become more prevalent, creating new attack vectors for cybercriminals. To address these concerns, healthcare organizations are investing heavily in advanced cybersecurity solutions such as threat intelligence, risk management, and incident response services.
Country Insights
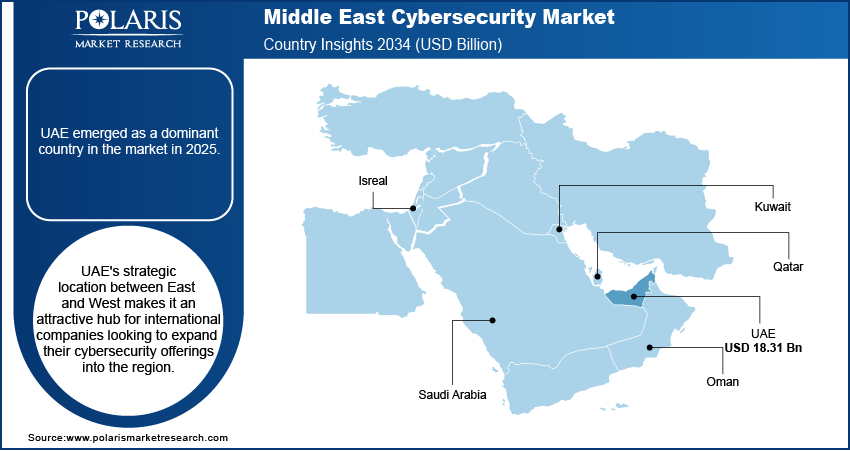
UAE
The United Arab Emirates (UAE) emerged as a dominant country in the market in 2025, owing to the country's high investments in digital transformation initiatives, including smart cities, IoT infrastructure, and cloud computing, which created a pressing need for robust cybersecurity measures. Also, the UAE government has been actively promoting cybersecurity awareness and adoption through various programs and regulations, such as the National Cyber Security Strategy and the Dubai Cyber Security Strategy. The country has established partnerships with leading global cybersecurity firms, fostering innovation and knowledge sharing.
Along with this, the UAE's strategic location between East and West makes it an attractive hub for international companies looking to expand their cybersecurity offerings into the region. As a result, many global players have set up operations in the UAE, further solidifying its position as a regional cybersecurity leader.
Competitive Landscape
Several key players, including both local and international companies, dominate the market. Middle East cybersecurity market major companies include IBM, Palo Alto Networks, and Cisco which has been active in the Middle East for many years. These companies have established themselves as leaders in the market through their extensive portfolios of security products and services, as well as their expertise in addressing the unique cyber threats faced by organizations in the region.
Some of the major players operating in the Middle East market include:
- Broadcom
- Check Point Software Technologies Ltd.
- Cisco Systems, Inc.
- CPX
- DTS Solutions, LLC
- Help AG
- IBM Corporation
- Palo Alto Networks
- Secureworks, Inc.
- Sophos Ltd.
- Trellix
Recent Developments
- In April 2025: UAE Cyber Security Council and Google Cloud opened a cybersecurity centre in Abu Dhabi to cut regional losses by USD 6.8 billion.
- In March 2025: UAE government set public- and private-sector security targets after a global hack, strengthening critical systems.
- In February 2025: G42 bought CPX Holdings to add complete security across its AI operations.
- In February 2025: Saudi company Cipher raised USD 13.3 million to expand security assessment and response services.
- In February 2024: Cisco revealed its intention to establish a new on-premises cloud data center in the United Arab Emirates. This new facility is set to cater to the company's Duo multifactor authentication (MFA) and secure access solution.
- In June 2023: Help AG unveiled its new integrated cyber defense platform known as Unify, which is designed to deliver a unified customer experience across all of the company's offerings.
- In December 2023: Mindware, a value-added distributor (VAD) operating in the Middle East and Africa, formed a strategic alliance with Vectra AI. This company leverages artificial intelligence to detect and respond to cyber threats.
Report Coverage
The Middle East Cybersecurity market report emphasizes the UAE, Saudi Arabia, Israel, Egypt, and the Rest of the Middle East to provide a better understanding of the product to the users. Also, the report provides market insights into recent developments and trends and analyzes the technologies that are gaining traction around the region. Furthermore, the report covers an in-depth qualitative analysis pertaining to various paradigm shifts associated with the transformation of these solutions.
The report provides a detailed analysis of the market while focusing on various key aspects such as competitive analysis, component, deployment mode, organization size, security type, solution, end-user, and futuristic growth opportunities.
Report Scope
| Report Attributes | Details |
| Market size value in 2025 | USD 16.78 billion |
| Market size value in 2026 | USD 18.40 billion |
| Revenue Forecast in 2034 | USD 39.31 billion |
| CAGR | 10.00% from 2026 – 2034 |
| Base year | 2025 |
| Historical data | 2021 – 2024 |
| Forecast period | 2026 – 2034 |
| Quantitative units | Revenue in USD billion and CAGR from 2026 to 2034 |
| Segments Covered | By Component, By Deployment Mode, By Organization Size, By Security Type, By Solution, By End-User, By Country |
| Country scope | UAE, Saudi Arabia, Israel, Egypt, Rest of Middle East |
| Customization | Report customization as per your requirements with respect to countries, regions, and segmentation. |
Want to check out the middle east cybersecurity market report before buying it? Then, our sample report has got you covered. It includes key market data points, ranging from trend analyses to industry estimates and forecasts. See for yourself by Download Sample Report.
FAQ's
key companies in Middle East Cybersecurity Market are Broadcom, Check Point Software Technologies Ltd., Cisco Systems, Inc., CPX, DTS Solutions
Middle East Cybersecurity Market exhibiting a CAGR of 10.00% during the forecast period.
The Middle East Cybersecurity Market report covering key segments are component, deployment mode, organization size, security type, solution, end-user, and country.
key driving factors in Middle East Cybersecurity Market are the growing number of cyber-attacks is driving the Middle East Cybersecurity market growth
The Middle East cybersecurity market size is expected to reach USD 39.31 Billion by 2034.
Download Sample Report of Middle East Cybersecurity Market
Please fill out the form to request a customized copy of the research report.